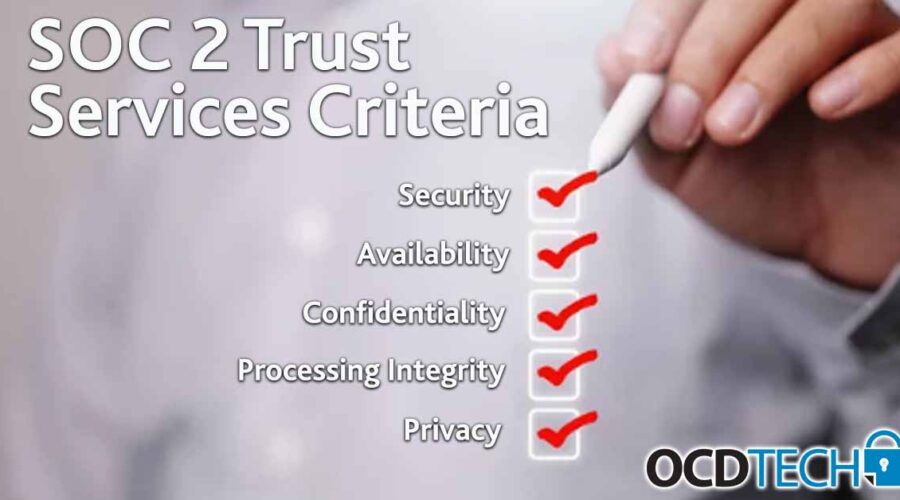
SOC 2® can apply to most service organizations, including companies who provide analytics, business intelligence, managed IT security service providers, […]
Though open source intelligence (OSINT) is often seen as a development of the modern age and the product of a […]
The Human Firewall
You’ve set up multifactor authentication and antivirus, enabled backups, secured physical devices and your WiFi, and you’ve spent hours configuring […]
In today’s digital world, it is more important than ever that organizations have comprehensive information security controls to maintain data […]
Why we Should be Concerned About Critical Infrastructure Vulnerabilities
CI) operators should increase their readiness for an attack. A CI disruption could bring the U.S. economy to a halt and previous attacks such as the Colonial Pipeline, JBS foods, and SolarWinds are testaments to the power of a well-executed cyber-attack.
SEC Proposed Rule Could Add Cybersecurity to the Boardroom
On March 9th, 2022, the Security and Exchanges Commission (SEC) issued several proposed amendments that could have a big impact on businesses.
If you feel like you’re hearing about ransomware attacks more often, you’re not wrong.
A South American-based hacking group that goes by LAPSUS$ has claimed responsibility for the recent cyberattack on Nvidia.
As with any “new” technology, there are always bugs and quirks, but unfortunately in the crypto world they are happening more and more.
The rapid advances in technology have created opportunities for businesses to realize new efficiencies and increased profitability.